Lee Neubecker: So HIPAA is the Health Insurance Portability and Accountability Act of 1996 and why this is important is all the hospital information system providers, have to certify that their software is HIPAA compliant. Otherwise, the hospitals receiving Medicare reimbursement wouldn’t be able to use the software. So, the presumption should be that any healthcare organization that is receiving Medicare funding is compliant with the rules of HIPAA and we’ll talk through what that requires here.
HIPAA Audit Trail Requirements: EMR / EHR
- Application audit trail audit trails
- EMR Opened / Accessed
- EMR Closed
- EMR Created
- EMR Edited (Original and Replacement Value) with last update time
- EMR Deleted
- System level audit trails
- Successful or unsuccessful logon event by username
- Date and time of each logon or logoff attempt
- Specific device used to logon
- Application user successfully or unsuccessfully accessed
- User audit trails
- Monitor and log user activity in an ePHI application
- Record events initiated by the user
- Commands directly initiated by the user
- Log access to ePHI files and resources
- Healthcare organizations must retain records at least six years
- States with stricter retention requirements must be honored
First, HIPAA requires that there be application audit trails that show when the EMR was open, accessed, closed, created, edited, the original value, replacement value, who updated it? When, from what computer, whether it was deleted? Your system-level audit trails, which has to do with the logons of the user to the system when they logged on, what computer was at the nurses’ station? Was it the computer that was actually bedside with the patient? So all of that can be relevant, especially in establishing whether or not a healthcare provider was with the patient at an important time.
User audit log trails monitor the user activity within a specific EPHI application. It records events, what commands were issued, and so on. Healthcare organizations must retain these records for at least six years and typically, if there’s an issue where litigation is involved at the point in time that they’re notified, their risk management committee will collect the records and make preservation of the available data. Some states have stricter retention requirements beyond six years and in those cases, the state rules should apply according to HIPAA.
HIPAA Audit Trail Requirements: Must Track
- Each time a user logins
- Whenever changes are made to databases
- When new users are added
- Access levels for each user
- File access by users
- Logins to operating systems
- Firewall logs
- Anti-malware logs
Other requirements of HIPAA include the following.
When a user logs on when changes are made to the databases, when users are added, access level for each user, what rights they have, the file access by the user. Logins to the operating system, firewall logs, anti-malware logs and more. So there’s a lot of requirements that hospitals are compliant and other health care organizations that are receiving Medicare funding follow these requirements.
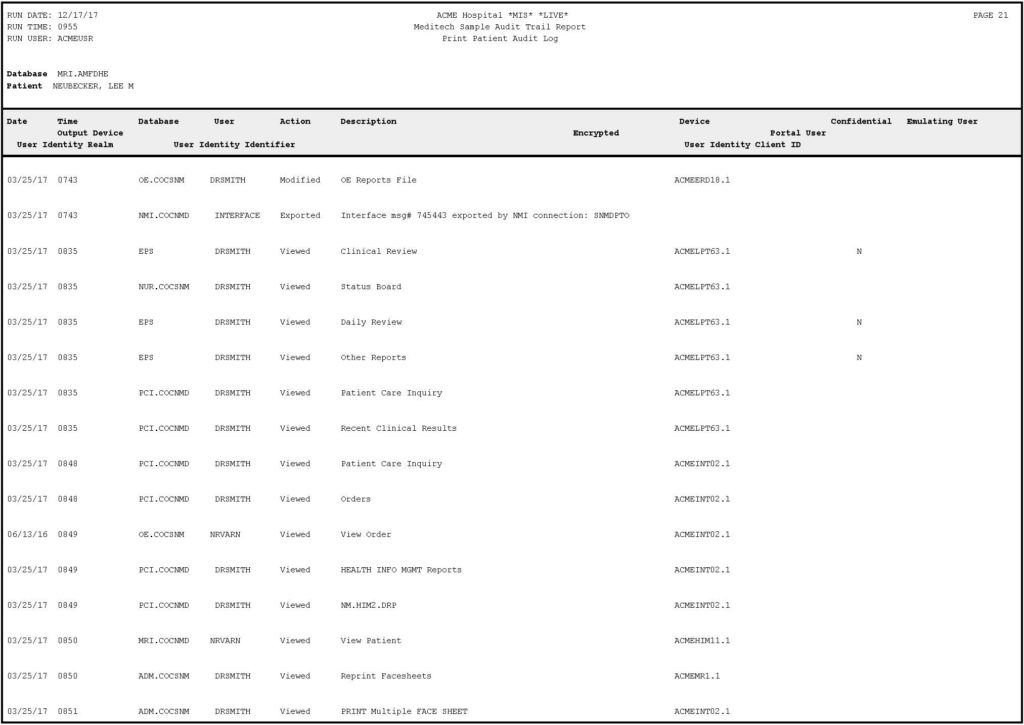
Example Audit Trail: Meditech
Lee Neubecker:
Here’s an example of what an audit trail log looks like. I know it’s probably a little bit difficult to see all of this but what we see, this one’s Meditech. What you’ll see here is there’s a run date, the date and time the report was run, the runtime, the username, the specific database being accessed, and who the patient was.
Then across the top, you have different data columns such as date, time, the user. What action, were they modifying, exporting, viewing? The description of the action? Then you have the device being used to access it. It also shows here that there’s a confidential flag and certain records which may or may not be produced.
And then there’s the ability for someone to, you know, Dr. Smith could enter something and emulate another user and you don’t often see the notion that someone else emulated another user when you’re viewing the progress note or printed chart. So the audit trail is important.
Now, unfortunately, this audit trail doesn’t show you the specific changes being made and oftentimes, what’s necessary is you actually have to get a direct in-camera inspection of the Meditech or other HIS system to be able to record and document what the care provider sees.
Watch other videos making up this 4 part series, Unlocking the EMR Audit Trail.
| Part 1 of 4: “The Keys to Unlocking Electronic Medical Records” https://enigmaforensics.com/blog/keys-to-unlocking-the-emr-audit-trails-electronic-medical-records/ |
| Part 2 of 4: “HIPAA” https://enigmaforensics.com/blog/health-insurance-portability-and-accountability-act-of-1996-hipaa/ |
| Part 3 of 4: “Navigating to Trial or Settlement” https://enigmaforensics.com/blog/navigating-to-trial-or-settlement/ |
| Part 4 of 4: “In-Person Direct Access” https://enigmaforensics.com/blog/in-person-direct-access-provides-additional-information/ |




