Cook County Circuit Court Judge James N. O’Hara wrote a Memorandum Order for the case of Angela Prieto vs. Rush University Medical Center (“RUMC”) and other defendants. The 23-page order highlights some important federal statutes, such as HIPAA and the HITECH Act. This established a legal basis for a plaintiff to receive their complete electronic medical record. Judge O’Hara implements a severe sanction that effectively was a default judgement leaving only the dollar amount of financial award to be determined by the jury.
Case Background
Plaintiff, Angela Prieto, on behalf of her son alleged that RUMC “negligently caused [her son] to suffer from hypoxic ischemic encephalopathy and respiratory distress syndrome during birth.” The case was originally filed in 2018. The request for production of electronic health records was originally filed in January of 2019. Plaintiff requested RUMC to produce the complete and unaltered EMR and audit trail. As of January 2022, there were three repeated requests from Prieto for RUMC to produce the complete EMR audit trail.
Audit Trails in EMR
The use of Electronic Medical Records (“EMR”) also known as Electronic Health Records (“EHR”) is mandatory to comply with requirements that health care providers maintain electronic medical records for patients. Every hospital, doctors office, or any medical practice in the United States must be compliant. The transition to using EMR began in 1992. Electronic medical records became mandatory since the start of 2014 through the American Recovery and Reinvestment Act.
All EMR systems are required by federal law to have an audit trail system built in. Audit trails show any deletions or edits that may not be part of the finalized medical record. A complete EMR audit trail shows all entry, access or modifications made to a patient’s chart. EMR audit trail productions should include all available records from the initial patient encounter until the date of production.
Audit Trail Manipulation
Health care providers often limit their production of audit trail records to the date the patient left the health care facility. However, this practice is problematic. When a patient’s EMR is modified after a Plaintiff files litigation and requests their complete EMR with audit trail records, manipulation of the Plaintiff’s medical records after that date can’t be detected. It is a common practice for healthcare providers to only produce the finalized patient EMR chart. This omits the revision history, a clear indicator of when the patient’s EMR was modified, by whom, from where, what time, and the specific redline changes that were made, as is required by any HIPAA compliant EMR system.

Electronic Health Records and EMR revision history must be retained by any HIPAA compliant EMR software system.
As Judge O’Hara put it in his order, “The term ‘Audit Trail’ refers to the part of the patient’s EHR that displays any person logging in to the record to modify the record, correct the record, add to the record, alter the record, revise the record, complete the record, put finishing touches on the record, and any other entry or access into the medical record, or any other name synonymous with the reflection of who, when and what a person did in relation to the Electronic Health Record.”
Request for ‘a complete, unaltered EHR Audit Trail’
He went on to discuss the EMR audit trail request in this specific case stating, “…requests asked for ‘a complete, unaltered EHR’…Prieto also requested ‘a complete, unaltered Audit Trail… in native format.’” This is a typical wording of requests for EHR or EMR Audit Trails that many healthcare providers fail to produce the first time. Instead, healthcare providers often send incomplete audit trails filtering out certain information.
…inspection revealed many aspects of the audit trail and EHR discovery that were either withheld, misrepresented or otherwise not produced…
Judge James O’Hara
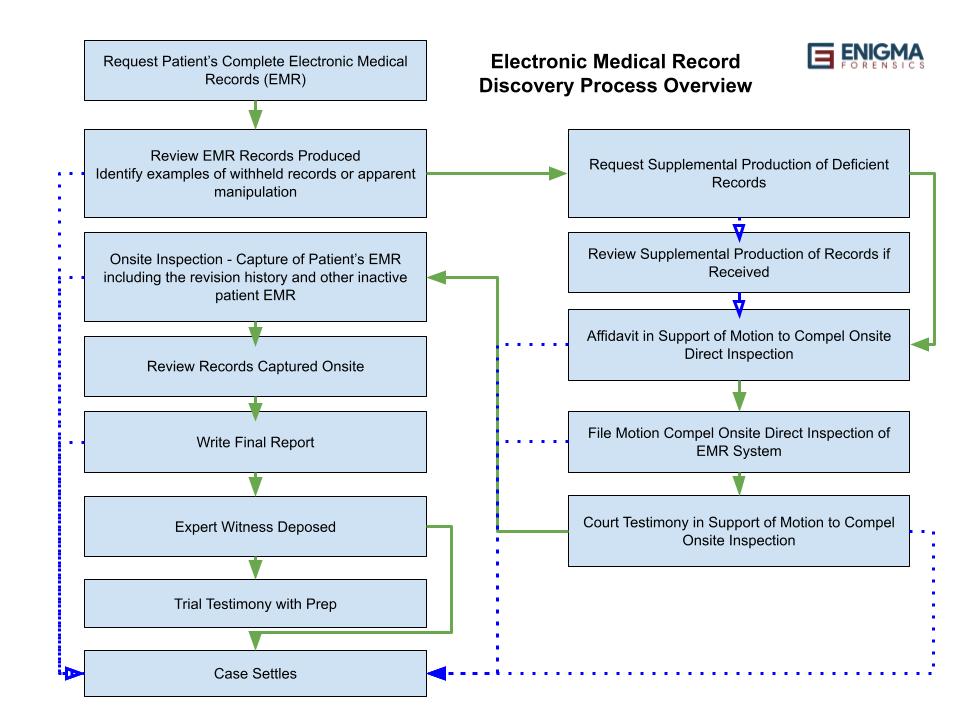
When the Defendant in this case failed to produce the Plaintiff’s complete electronic medical records, including a complete audit trail and EMR revision history as requested, Judge O’Hara granted “a motion for in camera, on-site inspection of the auditing systems at RUMC…” Judge O’Hara actually attended the onsite inspection himself. The date for the on-site inspection with the judge was set and O’Hara wrote of it, “…inspection revealed many aspects of the audit trail and EHR discovery that were either withheld, misrepresented, or otherwise not produced…”
Federal Laws Pertaining to EHR Audit Trail Production
HIPPA
Judge O’Hara listed the federal law governing audit trails. “Congress enacted the Health Insurance Portability and Accountability Act (“HIPAA”) to ‘improve the efficiency and effectiveness of the health care system, by encouraging the development of a health information system through the establishment of standards and requirements for the electronic transmission of certain health information,’” O’Hara quoted from HIPAA. He then continued, “In response to HIPAA, the Department of Health and Human Services (“HHS”) published HIPAA’s right of access rule: ‘Except as otherwise provided… an individual has a right of access to inspect and obtain a copy of protected health information about the individual in a designated record set, for as long as the protected health information is maintained in the designated record set.’”
HITECH & THE Cures Acts
O’Hara went on to quote, “the HITCH Act in 2009, Congress ‘expanded HIPAA to include individuals’ rights to obtain electronic health records and added a stronger privacy and security requirements to protect health information.’” He continued on, “The Cures Act would later respond to a growing concern that healthcare software developers and provided sought to restrict the amount and types of information accessible to individuals by adding ‘information blocking’ provisions – to further encourage the broad access to patients’ own health information.” Healthcare providers often cite the “Designated Record Set” as not including the EMR audit trail or revision history.
U.S. Department of Health and human services (“HHS”)
Judge O’Hara continued to quote the rules of HHS in regards to a patient’s EHR audit trail production, “‘Individually identifiable health information’ is further defined as information created by a health care provider that relates to the provision of health care to an individual, among other things, that can be used to identify the patient. Id. In sum, audit trail information is included in the patient’s right of access if it is created or used by the healthcare provider, can be used to help treat or identify the patient, relates to the provision of health care to the patient, and is maintained in electronic media.”

The Alleged Burden of Producing the Complete Medical Record
The supposed time burden for the medical facility to produce the EHR Audit Trail and revision history is a major objection provided to the court as a defense to the request for a Plaintiff’s complete electronic medical record. Judge O’Hara addresses that point in stating, “HHS has acknowledged that this imposes a heavy burden on healthcare providers… However, the national policy is that this burden cannot overcome the patient’s right of access… HHS went even further to impose a scheme of penalties for entities that disobey this national policy.”
Federal law says that audit trail data… is included in the patients right of access
Judge James O’Hara
Judge O’Hara finalized his section on the law by stating, “In sum, federal law says that audit trail data, including metadata associated with a patient’s EHR, is included in the patient’s right of access and that it constitutes information blocking to refuse to produce such data.”
Read the full order here: https://www.famjustice.org/_files/ugd/06ff46_3a6bcab463544b8b97bb10e7249405d8.pdf