As a Cyber Security company, Enigma Forensics is always interested in the 4W’s and 1H of a Cyber Attack. We would be remiss if we didn’t write a post about the most recent SolarWinds Hack allegedly by the Russians. Did the Russians time this cyber attack at precisely the moment in time when the United States is preoccupied? Amidst the Coronavirus shutdowns, the election results, the holidays, and the COVID-19 relief plan, it’s almost as if this particular Russian Hack completely flew under the radar.
What happened?
The attackers gained entry by using a software update sent out by Texas-based software company SolarWinds, which counts multiple U.S. government agencies as customers. In early December 2020, the news media reported at least 200 organizations, including U.S. government agencies and other companies around the world, have been hacked as part of this suspected Russian cyber attack.
Government’s response
The New York Times reported on December 13, 2020, “The Trump administration acknowledged on Sunday that hackers acting on behalf of a foreign government almost certainly a Russian intelligence agency, according to federal and private experts — broke into a range of key government networks, including in the Treasury and Commerce Departments, and had free access to their email systems.” We can’t find any reporting on what information was stolen.
Who raised the alarm?
It looks like FireEye, a computer security firm first raised the alarm about the Russian cyber attack after its own systems were compromised back in early Spring of 2020. What perfect timing to stage an attack considering the whole country is preoccupied with the rise of the pandemic! FireEye discovered a supply chain attack that was accessed through SolarWinds Orion business software updates in order to distribute malware that they called “SUNBURST.” Experts agree this is the work of highly-skilled actors and was performed with significant operational security. But, the real issue is why didn’t the government cyber protection agencies that are sworn to protect recognize the breach? It took an outside company to inform them of the cyber attack.
Where was the Cyber Attack aimed?
In this case, the U.S. government agencies seemed to be the target. As noted before, the hack was done through what is called a “supply chain attack,” in which malicious code is hidden in legitimate software updates and meant to target third parties. Could it have been the Chinese masquerading as the Russians? President Trump laid claim that there was potential it could have been the Chinese and not the Russians.
When was the Attack Noticed?
As reported by the New York Times, in a statement after a briefing for committee staff members, Senator Ron Wyden of Oregon, who has often been among the sharpest critics of the National Security Agency and other intelligence agencies, said that the Treasury Department had acknowledged that “the agency suffered a serious breach, beginning in July, the full depth of which isn’t known.” But no one will say just how serious the breach was!
Today, as reported in the Hill, the headline reads, “Intel vice chair says government agency cyber attack ‘may have started earlier’.” Sen. Mark Warner (D-Va.), the vice-chairman of the Senate Intelligence Committee, said on Wednesday, December 30, 2020, that the cyberattacks on U.S. government agencies reported at the beginning of the month may have begun earlier than previously believed.
How did the Hackers Hack?
The hackers used malicious code inserted into legitimate software updates for the SolarWinds Orion software. This allowed the hacker to remotely access the victim’s electronic environment. In order to avoid detection, they used a very small footprint and went to significant lengths to lay low and blend in. Very stealth-like in nature! The malware attacked slowly and moved with precision, covering its tracks and using tools that were hard to detect. Does this sound familiar?



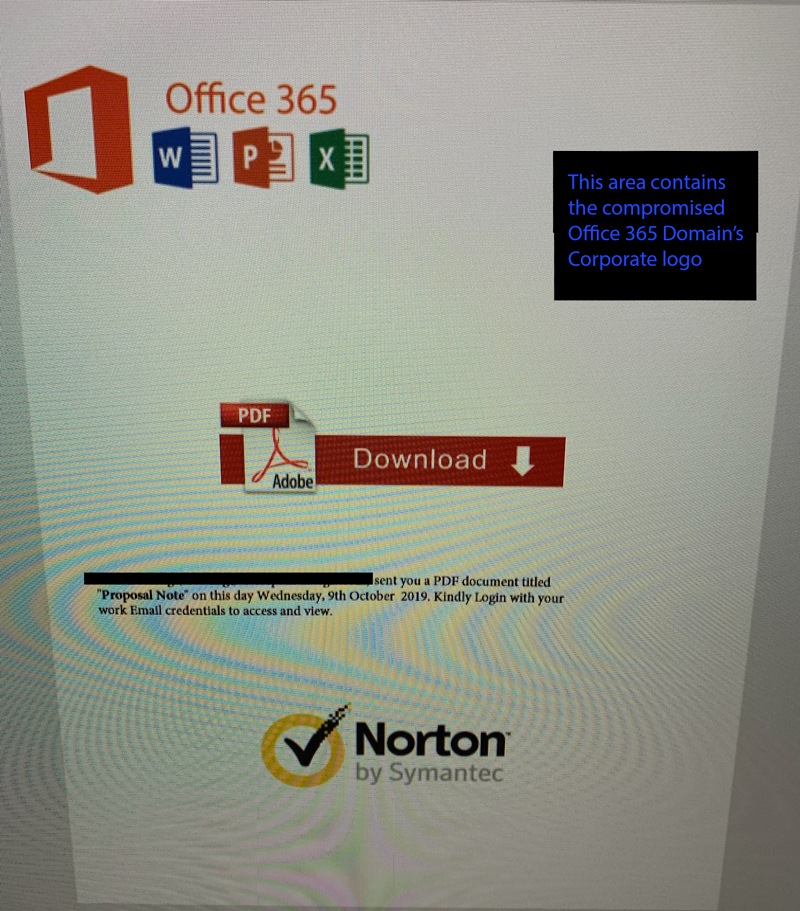 We have observed both the original inbound attachment and the outbound attachment that gets sent onward to the compromised user’s address book. Thus far, only users of Office 365 appear to be targeted. It appears that the malware checks the compromised user’s contacts and performs an mx record query to determine which contacts in the compromised user’s contact address book are hosting their email with Microsoft.
We have observed both the original inbound attachment and the outbound attachment that gets sent onward to the compromised user’s address book. Thus far, only users of Office 365 appear to be targeted. It appears that the malware checks the compromised user’s contacts and performs an mx record query to determine which contacts in the compromised user’s contact address book are hosting their email with Microsoft.