Enigma Forensics CEO & President Lee Neubecker attends Legal Tech 2018 in New York. Lee sits down with Attorney David Rownd who is a partner at Thompson Coburn to discuss trade secret misappropriation and the role of Computer Forensics. They share their experiences in litigation concerning trade secrets and the misapporiation of information.
The transcript of the video follows
Lee Neubecker: So I’m at LegalTech New York and I’m here with David Rownd. He’s a partner at Thompson Coburn and David and I had a past working on cases involving trade secret theft and misappropriation and I just asked him to come here today and share a little bit about his experience using computer forensics and what role that’s played in cases and helping him to get good results for his clients.
David Rownd: Well computer forensics can be an amazing tool, particularly in a trade secret misappropriation case where a departing employee takes valuable company information. Often almost all of the information that is relevant to a company’s business is stored on the computer and the most common situation that you see is where the employee mistakenly believes that no one will catch him if he just emails stuff to a personal account and that is, at this point a well-worn trick, but it still happens. And most employees, what they are doing, is a see that they are going to pursue another option and they want to use information that belongs to the company so they do what they can to obtain that information. And they may realize that it’s traceable, but they may not. But what they probably don’t realize is the extent to which it really is traceable. And that every little move can be captured with a forensics expert such as me.
Lee Neubecker: Thank you. So are there any recommendations you’d have to clients that have an employee that leave that might have sensitive client data and trade secrets? What would you advise those clients to do?
David Rownd: You mean before they leave or after they leave?
Lee Neubecker: They find out their Head of Sales and Marketing leaves and goes to a competitor, how would you advise that client if they called you up and said, Dave, what should we do? We’re concerned that this person took stuff.
David Rownd: Well, first of all, any computerized data, if there was a desktop computer that that employee worked at, you should immediately evaluate the desktop computer to see if in fact any data has been moved or transferred in any way. And there are a variety of different ways that it can be done. And you know better than I do all of those different ways to identify the potential use of data. There’s also the issue about what information may be on your iPhone or a handheld device. I mean those are more and more becoming part of the way business gets conducted, especially in terms of sales, these salespeople are on the road, they’re communicating with customers by text, by email, and being able to trace the activity that went on on personal handheld devices is obviously an important thing to do as well. And to try to get a grip on, okay, what exactly did this person do prior to leaving?
Lee Neubecker: Now, have you ever had a company call you up where they hired this person who left and took stuff?
David Rownd: Oh that happens all the time. I mean the typical scenario is, in a lawsuit such as this, is that the departing employee and the new employer are both named as defendants, and the new employer can be potentially aiding and abetting the misappropriation of information, they can be tortuously interfering with agreements that the departing employee had with his prior employer. And you know one of the things we didn’t talk about is what sort of agreements are these employees operating under? Good prevention measures obviously to have an employment agreement with people who are going to have sensitive, proprietary information where they acknowledge that the information is confidential and that it’s proprietary and that it’s valuable.
Lee Neubecker: And just to add Dave, one of the most important things before, if an employee is leaving, you want to make a forensic image as soon as possible, done in an appropriate matter so that the data doesn’t get altered ’cause that can introduce chain of custody attacks
David Rownd: Correct
Lee Neubecker: and other allegations.
David Rownd: Correct. And the quicker that’s done and the more process oriented the way that it’s done, the better because you’re going to want to ultimately demonstrate to a court that this is reliable and that’s the key. And so if you can show that it was done almost contemporaneously and if you can a show a step by step process by which this mirror image was created so that a court can look at that data and say yes, this is in fact what was in existent at that time.
Lee Neubecker: Can you tell us what other type of case matters you work on to help your clients? Just a little bit more to our viewers about your practice?
David Rownd: Well my practice is, I am a business litigator is the generic term, but that can mean a lot of different things. I’ve done a lot of trade secret misappropriation in the past. These cases with a departing employee goes to a new employer, I’ve been on all sides of those cases in the past. A lot of my work is business to business litigation where it’s centered around some sort of business arrangement usually documented by a contract, but there can be other issues which are extraneous and in your typical straight up litigation matter today, the importance of electronically stored information is significant because that’s the way we do business now.




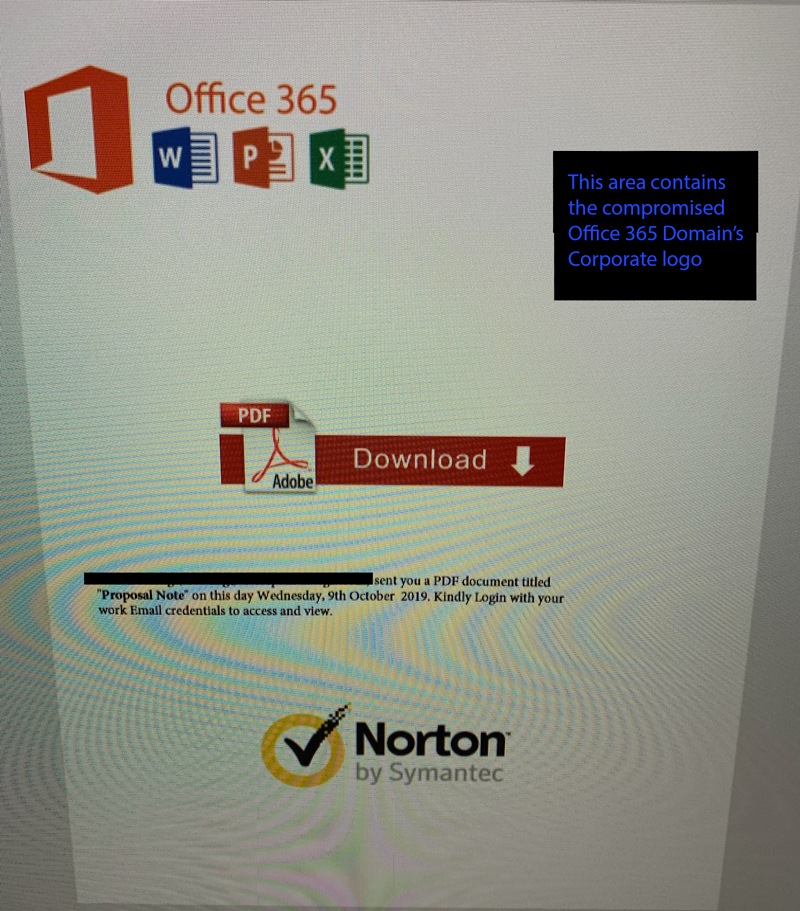 We have observed both the original inbound attachment and the outbound attachment that gets sent onward to the compromised user’s address book. Thus far, only users of Office 365 appear to be targeted. It appears that the malware checks the compromised user’s contacts and performs an mx record query to determine which contacts in the compromised user’s contact address book are hosting their email with Microsoft.
We have observed both the original inbound attachment and the outbound attachment that gets sent onward to the compromised user’s address book. Thus far, only users of Office 365 appear to be targeted. It appears that the malware checks the compromised user’s contacts and performs an mx record query to determine which contacts in the compromised user’s contact address book are hosting their email with Microsoft.